
微信扫一扫联系客服
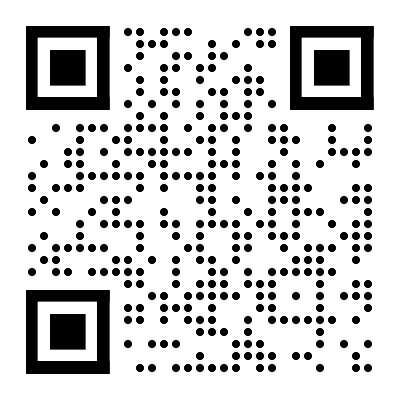
微信扫描二维码
进入报告厅H5

关注报告厅公众号
This proposal is part of the EU Security Union Strategy1 adopted by the Commission on 24 July 2020 and laying down its commitment to bring the European Union's added value to the national efforts in the area of security. Part of this engagement is the initiative to streamline the internal legal frameworks for information security in all Union institutions and bodies.
A key feature of the Strategic Agenda for 2019-2024 adopted by the European Council in June 2019 is to protect our societies from the ever evolving threats targeting the information handled by institutions and bodies. In its conclusions2, the European Council called in particular on ‘the EU institutions, together with the Member States, to work on measures to enhance the resilience and improve the security culture of the European Union against cyber and hybrid threats from outside the EU, and to better protect the EU’s information and communication networks, and its decision-making processes, from malicious activities of all kinds’.
In the same line, the General Affairs Council of December 20193 concluded that the EU institutions and bodies, supported by Member States, should develop and implement a comprehensive set of measures to ensure their security. This echoes a long standing request from the Council Security Committee to investigate a common core of security rules for the Council, the Commission and the European External Action Service4.
Currently, the Union institutions and bodies either have their own information security rules, based on their Rules of procedure or founding act, or they do not have information security rules at all. This is mostly the case of some small entities, which lack any formal information security policies.
Due to the ever-increasing amounts of sensitive non-classified and European Union classified information (‘EUCI’) that the Union institutions and bodies need to share between themselves and considering the dramatic development of the threat landscape, the European administration is exposed to attack in all its areas of activity. The information handled by our institutions and bodies is very attractive for the threat actors and needs to be appropriately protected. This requires swift action aiming at enhancing its protection.
相关报告
2022西湖论剑大会专家演讲PPT合集(22份)
4931
类型:IT互联网
上传时间:2022-07
标签:信创、网络安全、智能)
语言:中文
金额:免费
国家电网-新一代信息通信及网络安全技术发展趋势
3297
类型:行研
上传时间:2020-12
标签:信息通信、网络安全)
语言:中文
金额:5积分
计算机行业安全服务:网络安全行业的制高点-20210221-方正证券-64页
2380
类型:行研
上传时间:2021-02
标签:计算机、网络安全)
语言:中文
金额:免费
网络安全IT路线图
2357
类型:行研
上传时间:2021-03
标签:网络安全、IT)
语言:中文
金额:免费
中国网络安全产业白皮书
2060
类型:行研
上传时间:2022-01
标签:网络安全)
语言:中文
金额:免费
2023全球网络安全前瞻调研报告
1892
类型:行研
上传时间:2023-07
标签:网络安全、互联网、信息安全)
语言:中文
金额:5积分
中国网络安全产业白皮书(2020年)
1825
类型:专题
上传时间:2020-09
标签:网络安全、白皮书)
语言:中文
金额:5积分
复旦发展研究院:重点国家网络安全立法洞察报告
1820
类型:专题
上传时间:2020-10
标签:网络安全、立法)
语言:中文
金额:5积分
图解-网络数据安全风险评估实施指引V1.0
1736
类型:专题
上传时间:2023-06
标签:网络安全、数据安全、互联网)
语言:中文
金额:5积分
信息安全技术网络安全等级保护大数据基本要求
1688
类型:经管职场
上传时间:2021-05
标签:网络安全、大数据)
语言:中文
金额:免费
积分充值
30积分
6.00元
90积分
18.00元
150+8积分
30.00元
340+20积分
68.00元
640+50积分
128.00元
990+70积分
198.00元
1640+140积分
328.00元
微信支付
余额支付
积分充值
应付金额:
0 元
请登录,再发表你的看法
登录/注册